CyberFactory#1: Präsentation der Ergebnisse in Finnland
Das Webinar bietet Einblicke in die Forschungs- und Entwicklungsarbeit der finnischen Konsortialpartner Bittium, High Metal, Houston Analytics, Netox, Rugged Tooling und VTT während der letzten drei Jahre. Wir konzentrieren uns auf die Kernthemen des ITEA-Projekts, nämlich Optimierung und Cybersicherheit. Das Webinar beginnt mit einer kurzen Einführung in das Projekt durch den Gastgeber Jarno Salonen (Senior Scientist und Landeskoordinator des CyberFactory#1 Projekts). Danach stellen die Partner ihre wichtigsten Projektergebnisse vor.
Aufnahme:
Die Hauptsprache der Veranstaltung ist Finnisch.
Präsentationen
Webinar kick-off. What is CyberFactory#1 about?
Jarno Salonen, VTT
Lauri Nurminen, High Metal
Quality assurance and monitoring of demanding IP networks in lab and live
Risto Kauppi, Rugged Tooling
IAM approaches in factory environments
Markku Korkiakoski, Netox
AI utilization for anomaly detection in cybersecurity
Antti Syväniemi, Houston Analytics
Digital Twin for industrial cybersecurity simulations
Mirko Sailio, VTT
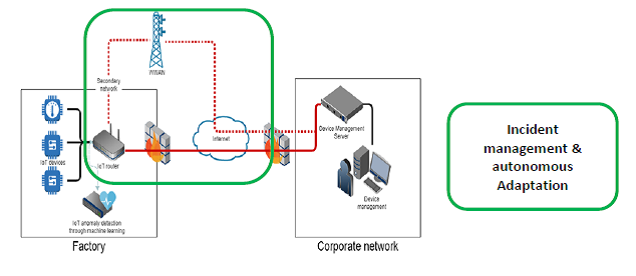
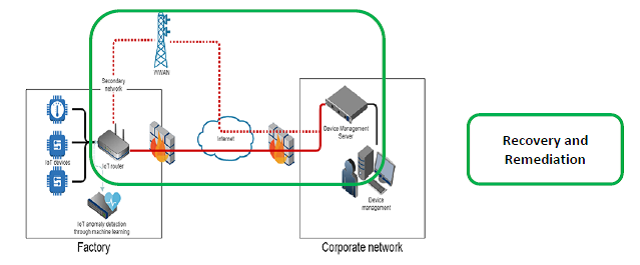
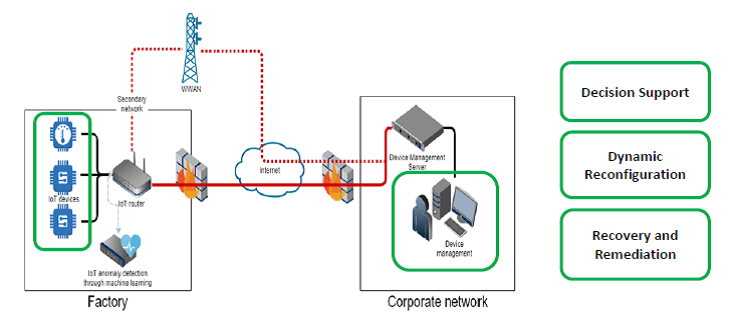
Development of Cybersecure Architecture to improve Cyber Resilience – Practical Examples
Jari Partanen, Bittium
Webinar conclusion and final words
Jarno Salonen, VTT
Sprecher
Jarno Salonen ist Senior Scientist im Forschungsteam für angewandte Cybersicherheit bei VTT. Er ist der finnische Landeskoordinator von CyberFactory#1 und koordiniert außerdem die Forschung von VTT in drei anderen EU-Projekten: SeCoIIA, CyberSec4Europe und Mind4Machines. Er verfügt über eine beruflichen Laufbahn von mehr als 20 Jahren, in denen er die digitale Welt zu einem besseren Ort für normale Nutzer gemacht hat, insbesondere in den Bereichen Cybersicherheit, Datenschutz, Widerstandsfähigkeit und Entwicklung digitaler Dienste.
Lauri Nurminen ist Vizepräsident und Unternehmer des Familienunternehmens High Metal Oy. Bei High Metal ist er für das Marketing, den Vertrieb und das Projektmanagement von CyberFactory#1 verantwortlich. Er verfügt über mehr als 15 Jahre Berufserfahrung in der Umsetzung der Ideen von Ingenieuren bei Kunden. Sein Ziel ist es, ein traditionelles Fertigungsunternehmen in ein technologie- und datenorientiertes Unternehmen umzuwandeln.
Antti Syväniemi ist der CEO und Gründer von Houston Analytics Ltd. Antti Syväniemi verfügt über mehr als 15 Jahre Erfahrung in der Anwendung von Analyseverfahren auf Geschäftsprozesse. Vor der Gründung von Houston Analytics hatte Antti Syväniemi leitende Positionen in den Bereichen Geschäftsentwicklung, CRM, Kunden- und Marktintelligenz sowie Category Management inne. Zu Anttis Hauptschwerpunkten gehören analytikbasierte Managementmodelle und intelligente Strategieprozesse.
Mirko Sailio ist Wissenschaftler beim VTT Technical Research Centre of Finland und verfügt über mehr als 10 Jahre Erfahrung, wobei er sich auf die Überwachung der Netzsicherheit in komplexen Netzwerken konzentriert. Er interessiert sich für technische Sicherheit, Bedrohungsakteure und die Herausforderungen bei der Nutzung von KI/ML zur Erhöhung der Netzwerksicherheit.
Jari Partanen ist Direktor für Qualität, Umwelt und Technologiemanagement bei Bittium. Das Ziel von Bittium im Cyberfactory#1-Projekt war die Schaffung einer konsistenten und sicheren Informationsarchitektur, von Prozessen und Informationswerkzeugen, die eine partnerschaftliche Fertigung und Lieferung in Echtzeit ermöglichen, einschließlich verschiedener Produktunterstützungsdienste und damit verbundener Informationswerkzeuge. Jari Partanen ist seit über 20 Jahren in der Forschung tätig und hat über 20 wissenschaftliche Publikationen veröffentlicht. Zu seinen Forschungsinteressen gehören Themen wie Cybersicherheit, agile Softwareentwicklung, Methoden zur Wertschöpfung in Echtzeit, Methoden zur Nutzung von Innovationen sowie Techniken zur Massenanpassung. Jari Partanen ist aktiv an einer Vielzahl europäischer und finnischer Forschungsprojekte beteiligt.
Markku Korkiakoski ist der Chief Operating Officer bei Netox. Er ist verantwortlich für das Cyberfactory#1-Projektmanagement bei Netox. Markku hat mehr als 20 Jahre Berufserfahrung und ist ein aktives Mitglied im Bereich der Cybersicherheit, sowohl auf nationaler als auch auf internationaler Ebene. Er ist Mitglied des Vorstands des Finnish Information Security Cluster, Mitglied der Arbeitsgruppe der ENISA und Vorsitzender des Industry Advisory Board des SERC (I/UCRC, National Science Foundation program, FIN-USA).
Risto Kauppi ist CEO (act.) und Hauptpartner von Rugged Tooling. Seine Hauptaufgabe in CyberFactory#1 ist die Suche nach skalierbaren Geschäftsmöglichkeiten auf der Grundlage der Forschungsergebnisse des Projekts. Risto ist ein langjähriger Geschäftsmann mit 25 Jahren Erfahrung in internationalen Partnerschaften und Verhandlungen.
Falls Sie Fragen zu der Veranstaltung haben, kontaktieren Sie bitte Jarno Salonen.




 https://pixabay.com/photos/writing-write-person-paperwork-828911/
https://pixabay.com/photos/writing-write-person-paperwork-828911/